Stay informed with expert advice and insights on tech trends, IT solutions, cloud computing, VoIP, and managed services. Explore the simpleroute blog today!
Interested in working with us?

Stay informed with expert advice and insights on tech trends, IT solutions, cloud computing, VoIP, and managed services. Explore the simpleroute blog today!
Interested in working with us?

Microsoft has announced global price changes taking effect on July 1, 2026. Discover how these updates impact your M365 licensing, what new features are being bundled in, and how simpleroute can help you audit and optimize your IT spend to protect your bottom line.

Your team is likely using AI right now—but do you know which tools they’ve chosen? From data leaks to compliance gaps, "Shadow AI" is the hidden risk in modern workflows. Discover how to move your business from the shadows into a secure, governed future.
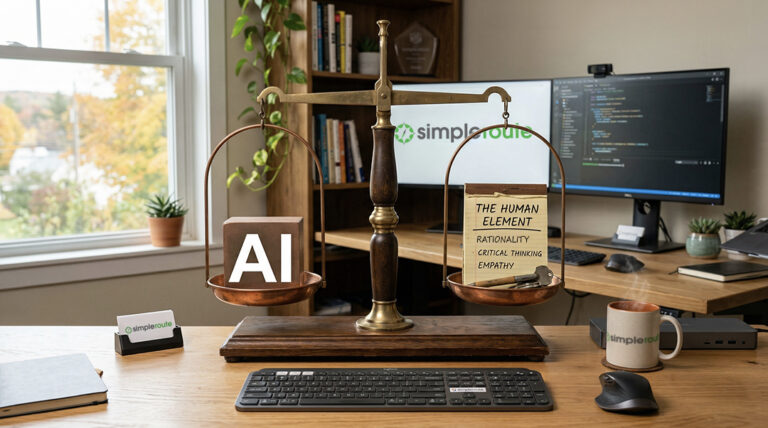
Thinking about bringing AI into your business plan? This post explores the powerful benefits—like efficiency and smarter data use—alongside the critical risks every business owner must navigate, including data privacy and the 'human element.' If you're looking for a balanced perspective on integrating AI, start here.

Business success requires treating technology as a tool, not just a cost. Managed IT services provide the strategic foundation needed to increase efficiency and maximize your ROI.
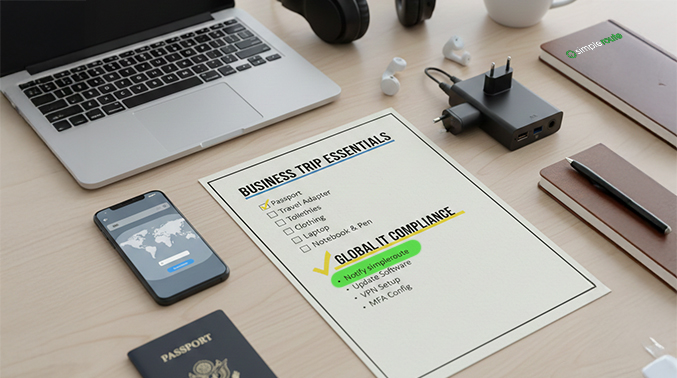
Plan your next trip with confidence. Get the essential international travel IT checklist from simpleroute to ensure secure remote access and compliance.

IMFA compliance for cyber insurance In the current business landscape, securing your organization requires…

The Green Mountain State’s manufacturing sector is vital. It provides stable, high-wage jobs across…

We are incredibly excited to share that simpleroute has officially relocated to a new,…

A wonderful turnout for simpleroute at the 2025 VT Tech Jam